
IdeaPad Notebooks, Feel Special When Your Laptop Greets Only You
 An innovative, international technology company that develops and manufactures cutting-edge, reliable, high-quality PC products and value-added professional services, Linovo presents new IdeaPad notebooks to those who are no more interested in ordinary products and search for something special.
An innovative, international technology company that develops and manufactures cutting-edge, reliable, high-quality PC products and value-added professional services, Linovo presents new IdeaPad notebooks to those who are no more interested in ordinary products and search for something special.According to LENOVO’s official web site, it emphasizes main features of the new product-IdeaPad notebooks; notebooks come with 17’’ and 15’’ widescreen displays. The main features that make IdeaPad different from the other ones are:
VeriFace™ facial recognition security
Dolby® Home Theater™ sound
Frameless screen
Multimedia Control Center with touch-sensitive buttons
GameZone keys with secondary display
 Lenovo promises comfort while opening the notebook and represents three varieties of the product. Choice of product type mostly depends on the demands of the clients and the consumers. IdeaPad is of three styles. These are: IdeaPad Y510, Mobile versatility that identifies 4 mains specific features. IdeaPad Y510 has an integrated 1.3 megapixel camera and Lenovo's VeriFace™ face recognition software. This is the unique feature that can make face your password and help control access to the notebook by the time the owner of the notebook sits at it. Despite the fact that the IdeaPad Y510 makes the user feel special the Dolby® Home Theater™ premium audio system attracts attention of the segment that is fond of theater-style sound. The product creates excellent entertainment environment with the help of Multimedia Control Center.
Lenovo promises comfort while opening the notebook and represents three varieties of the product. Choice of product type mostly depends on the demands of the clients and the consumers. IdeaPad is of three styles. These are: IdeaPad Y510, Mobile versatility that identifies 4 mains specific features. IdeaPad Y510 has an integrated 1.3 megapixel camera and Lenovo's VeriFace™ face recognition software. This is the unique feature that can make face your password and help control access to the notebook by the time the owner of the notebook sits at it. Despite the fact that the IdeaPad Y510 makes the user feel special the Dolby® Home Theater™ premium audio system attracts attention of the segment that is fond of theater-style sound. The product creates excellent entertainment environment with the help of Multimedia Control Center. The other style is IdeaPad Y710, Performance entertainment. This style is focused on the segment who is interested in advanced processing and graphics options for multimedia and gaming. Among the exceptional features of IdeaPad Y710 are 17’’ displays with frameless screen, VeriFace face recognition security, like the IdeaPad Y510 has, Dolby® Home Theater™ audio, and the different feature from the IdeaPad Y510 is that it has Secondary hard drive (optional).
The other style is IdeaPad Y710, Performance entertainment. This style is focused on the segment who is interested in advanced processing and graphics options for multimedia and gaming. Among the exceptional features of IdeaPad Y710 are 17’’ displays with frameless screen, VeriFace face recognition security, like the IdeaPad Y510 has, Dolby® Home Theater™ audio, and the different feature from the IdeaPad Y510 is that it has Secondary hard drive (optional). The third alternative of the IdeaPad that is coming soon is IdeaPad U110 Ultraportable style. And what are the specifics of this style? Well, as the official site of LENOVO claims the IdeaPad U110 is extremely thin and light for on-the-go people and who can not live without the one and who like to carry the best. Again as the previous two style Ideapads IdeaPad U110 has display with frameless screen but it is 11.1’’, the same VeriFace face recognition security, and Dolby® Home Theater™ audio, though Solid state hard drive (optional).
The third alternative of the IdeaPad that is coming soon is IdeaPad U110 Ultraportable style. And what are the specifics of this style? Well, as the official site of LENOVO claims the IdeaPad U110 is extremely thin and light for on-the-go people and who can not live without the one and who like to carry the best. Again as the previous two style Ideapads IdeaPad U110 has display with frameless screen but it is 11.1’’, the same VeriFace face recognition security, and Dolby® Home Theater™ audio, though Solid state hard drive (optional).  The latest version of web browser Firefox will make changes to the way people search for information online. The new browser has been designed around the importance of search to users. Firefox 3, currently going through its third stage of beta testing, will offer a combined search and bookmark tool via the url bar. It will also allow offline working.
The latest version of web browser Firefox will make changes to the way people search for information online. The new browser has been designed around the importance of search to users. Firefox 3, currently going through its third stage of beta testing, will offer a combined search and bookmark tool via the url bar. It will also allow offline working.Chairman of the Mozilla Foundation Mitchell Baker says: "It's clear that when people are looking for information on the web, search is the number one activity. We've devised ways to bring that power into areas that are closer to your individual life".
Typing "cameras", for example, into the url bar, will bring up a list of the sites that the user recently visited that have cameras in their names.
"If you buy a shoe, that’s all you need to remember - we will use search, as you've come to expect it, to help you find the places that you have been visiting," - says Ms Baker.
"It will be faster, sleeker, and even easier to use. In terms of features, we've tried very hard not to bloat the interface but to keep it simple, the way people like it, and to have new things appear when you need them." -she said.
The other substantial change will be the ability to do much more offline, with the browser "remembering" key data that is usually lost when an internet connection goes down. This is designed to allow the user to continue to work when traveling or in remote areas where wireless access is patchy. Firefox is currently the second most popular browser, although its 12% share is dwarfed by that of Microsoft's Internet Explorer. It has, however, substantially grown from its launch - first as
Ms Baker said that when Mozilla issued Firefox 1 they had one staff member, but hundreds working on different aspects of it. Now they have 150 employees around the world, and "tens of thousands" working on the software. Mozilla is run as a not-for-profit organization, and advocate of open source coding.
Also it is to admire that Mozilla Messaging; the new mail focused subsidiary of the non-profit Mozilla Foundation, has already begun operations on February 19. The initial focus for Mozilla Messaging is the development of Thunderbird 3, which will deliver significant improvements, notably integrated calendaring, better search and enhancements to the overall user experience.
“We're excited to renew the focus of our open source community on the future of Thunderbird. Each and every one of us is committed to building a great email product that people will love to use and that serves as the foundation for choice in a critical area of Internet software.” - said David Ascher, CEO, Mozilla Messaging.
“Thunderbird email is a vital part of the Mozilla project which brings freedom to hundreds of millions of internet users worldwide,” said Marten Mickos, CEO of
References:
http://www.mozillazine.org/talkback.html?article=23027http://www.mozillamessaging.com/en-US/news/
One of the most successful companies FERNBACH that claims to be the key players in the global Enterprise-wide Value and Risk Management industry for financial services that enhances this claim on the bases of FERNBACH’s achievement the growth rate of that is 20 per cent presents FlexFinance® Profitability. Software is the solution tool that will enable banks to manage the planning and budgeting process easier, and time efficiently. According to FERNBACH the software is expected to help banks make solutions in pricing, planning, internal reporting, and profitability analysis including product, organisational and customer analysis.
The analysis of gathered data includes the calculation of gross yields, net yields, and yields by products and customers. Software function is also Business Intelligence (BI). This function provides with the materials later used as reports.
Günther Fernbach, CEO of FERNBACH-Software, “FlexFinance® Profitability is a critical component for overall planning and profitability activities within financial institutions. Our solution supports the controlling processes that are responsible for corporate reporting by providing income and risk analyses which are instrumental in ensuring bank management processes and good governance.”
References:
http://www.fernbach.com/fs/en/home/news/26.02.2008_-_fernbach_launches_profitability_software.html
http://www.sourcewire.com/releases/rel_display.php?relid=iTXTz
http://www.bobhope.com/
 Adobe has launched software designed to make it easier for computer users to use online applications offline. Adobe Air allows developers to build tools that still have some functionality even when a computer is no longer connected to the net. A free download will allow users of Macs, PCs and, later this year, Linux machines to run any Air applications. The first programs that use the technology, developed by web sites such as eBay, have already been released.
Adobe has launched software designed to make it easier for computer users to use online applications offline. Adobe Air allows developers to build tools that still have some functionality even when a computer is no longer connected to the net. A free download will allow users of Macs, PCs and, later this year, Linux machines to run any Air applications. The first programs that use the technology, developed by web sites such as eBay, have already been released."Air is going to allow applications that run on the web today - that run in the browser - to be brought down to the desktop. It's about taking existing web applications and adding extra functionality whether you want to work offline or whether you want to access data on your disk " – says Andrew Shorten, platform evangelist at Adobe.
Mr. Shorten said that the technology is not about replacing the web browser: "It's about delivering the best experience depending on where you are and what you need to get from the application. If I'm on the road with my laptop maybe I want to use the desktop version of my application. If I pop into an internet cafe I can still access it through the browser."
The software is part of a growing number of technologies that aim to make the transition between the on and offline worlds seamless. In 2006, Microsoft unveiled its Silverlight technology. And last year http://www.google.com/ Google launched Gears.
The tool does not allow the creation of new content but does allow web applications to be used offline. For example, the developers of the free online office package Zoho use Gears to give users similar functionality to normal desktop office programs. Similarly, Adobe is looking into provide Air versions of many of its popular programs such as Photoshop. A host of other companies and web services have already built Air applications. For example, Ebay has built a program that allows users to do much of the legwork required in setting up auctions offline. The next time the user connects to the internet the listing would be posted to the website.
The application also allows users to keep up to date with auctions and bids without the need to have a browser open at the eBay page. The corporation is currently building prototype versions of several applications such as the news ticker, which displays headlines on a desktop, and mini Motty, which provides desktop football commentary. The current versions of the programs only work on PCs. Other programs exploit Air's ability to access both web content and files on a computer's disk. For example, the web-version of Finetunes allows users to stream music over the internet
"If you install the Air version on your desktop it can also look at what you have in your iTunes library and then suggest music based on what it finds. So it's really taking the essence of what works on the web, brining it to the desktop and then making it more personal to you " - explained Mr. Shorten.
Some commentators have pointed out that the ability for an application to delve between the web and a computer's hard drive raises security implications.
"Our advice would be to only install applications from sources that you trust," - said Mr. Shorten.
Corporate Telecommunications presents the service that gives the users opportunity to diagnose their headsets: who is using which headset, which ones need repairing, which are out of warranty, which ones need new voice tubes or need upgrading. These are achieved by unique identity codes and specially-designed software that monitor the lifecycle of each headset.
Access to information does not require separate software. It is automatically stored on a secure web-based database. All changes are updated directly onto the system.
Chan Bansal, business development manager at Corporate Telecommunications said: "Trying to keep track of headsets using an Excel spreadsheet or databases might work in the short term, but manually inputting information on scores of headsets is a time consuming task. And if the administrator is on holiday, sick or leaves the company, it doesn't take long for the spreadsheet to become out of date. Not to mention the security risks of losing potentially sensitive information."
A comprehensive audit trail for each headset, with multiple reporting options is provided by Accucheck software. A history of each change in use or status is created for both headsets and agents.
Bansal announces that "Developments in business culture, such as health and safety laws, regulatory changes and tight cost controls, mean sketchy asset records are not acceptable. Not managing your assets effectively, wastes time, costs money and risks falling foul of regulations."
 Apple (AAPL) shares are down sharply to their lowest level since June, as several analyst reports have triggered fresh concerns about the state of demand for iPhones and iPods.
Apple (AAPL) shares are down sharply to their lowest level since June, as several analyst reports have triggered fresh concerns about the state of demand for iPhones and iPods.Toni Sacconaghi, an analyst at Bernstein Research, has published the transcript of a recent conference call he held with investors on the subject of unlocked iPhones, what they mean to Apple, and what options the company has to deal with them. In a summary of the call, he contends that, while the iPhone has the potential to drive material earnings growth for Apple, the company faces two “significant challenges”: demand appears to be falling short of expectations, and the incidence of unlocking is much higher than expected.
Sacconaghi admits that the iPhone will be 6% of Apple’s revenues in FY ‘08, but could be nearly a quarter of the total by FY 2012, driving half of the company’s revenue growth over the next four years; and he notes that since the iPhone has a higher gross margin than other Apple products, it could drive 70%-80% of the company’s profit growth.
Sacconaghi says that weekly run-rate sales in the December quarter were about 180,000 units or less than 10 million on an annualized basis in the busiest quarter of the year for consumer electronics sales. That leads him to conclude that the goal of selling 10 million units in 2008 is optimistic, “particularly if Apple insists on carrier revenue-sharing, without significant price cuts or new model introductions.” He says European sales of the iPhone have been “particularly disappointing,” falling short of carriers’ initial expectations. Sacconaghi is projecting 1.45 million units in the December quarter, 6.9 million for the September 2008 fiscal year and 7.9 million for calendar 2008.
Sacconaghi, who kicked off the “missing iPhones” debate in January, pointing out the wide gap between the number of iPhones Apple has sold and the number of iPhone customers AT&T (T) as the exclusive U.S. carrier has signed up, repeats his previous estimate that 25%-30% of iPhones sold to date have been unlocked for use with carriers other than the one authorized by Apple. He notes that, if Apple sold 10 million iPhones this year but 30% were unlicked, the company would be losing out on $1.1 billion-$1.3 billion of revenue and 80-85 cents a share in EPS over the following two years. He also notes, not for the first time, that the unlocked phones pose a strategic issue, limiting the company’s ability to provide a truly exclusive relationship to carriers, and so reducing their willingness to kick back some subscriber revenue to Apple in return for an exclusive deal.
J.P. Morgan’s Bill Shope on Friday wrote that “with relatively slow unit growth in the holiday season” and the recent price cut for the iPod Shuffle, “signs point to iPod saturation and some macro sensitivity.” He says the Shuffle price cut “is likely intended to boost Shuffle momentum and iPod units overall.” In a separate note, Shope also says that Apple “still seems comfortable with Mac momentum, which remains the critical component of the story at these levels.” He says that Apple execs in a recent meeting would not comment on iPod and iPhone demand concerns, but did say that Mac product family is better positioned than in the last economic downturn.
Morgan Stanley noted Friday that MacBook distributor inventories are “near all-time lows” for the third straight week, but that iMac units are above historical average levels. The iPod Touch, they say, is selling well, with low channel inventory, while Shuffle inventory, which had accumulated in recent months, is down sharply ahead of the arrival of recently unveiled 2GB model.
The iPhone is an Internet-enabled multimedia mobile phone designed and marketed by Apple Inc. It has a multi-touch screen with virtual keyboard and buttons. The iPhone's functions include those of a camera phone and a portable media player ("iPod"), in addition to text messaging and visual voicemail. It also offers Internet services including e-mail, web browsing, and local Wi-Fi connectivity. It is a quad-band mobile phone that uses the GSM standard, and hence has international capability. It supports the EDGE data technology.
Following the success of iPods, Apple announced the iPhone in January 2007. The announcement was preceded by rumors and speculations that circulated for several months. The iPhone was introduced, first in the
 The first Academy Awards that was handed out on May 16, 1929, continues and celebrates its 80th Jubilee. It might be surprising but the ticket of the ceremony cost just $5 the first time, and was held in the Blossom Room of the Hollywood Roosevelt Hotel. From the very beginning the ceremony was filled with speeches, as for the statuettes. They were handled by Academy President Douglas Fairbanks.
The first Academy Awards that was handed out on May 16, 1929, continues and celebrates its 80th Jubilee. It might be surprising but the ticket of the ceremony cost just $5 the first time, and was held in the Blossom Room of the Hollywood Roosevelt Hotel. From the very beginning the ceremony was filled with speeches, as for the statuettes. They were handled by Academy President Douglas Fairbanks.According to Oscar’s official web site the Academy's general goal is the advancement of the arts and sciences of motion pictures. The fulfillment of this goal was achieved by hard work of following people, and the Oscar went to...
Best Motion Picture: "No Country for Old Men."
Today Oscar is not only ceremony where artists are awarded for their work but it is much more. Red Carpet represents Oscar Ceremony as one of the impressive, glittering shows of style, fashion, taste.
And those who could not watch the ceremony on the 24th of February Oscar official web site presents the Red Carpet of 2008. That is the charm of the World Wide Web.
Internet protocol (IP) worms;
Disruption of the IP network and denial of service;
The harvesting of consumers’ transaction data for malicious purposes
The harvesting of consumers’ transaction data for malicious purposes gives opportunities to hackers collect consumers’ personal details, their card number, account balance and transaction history.
According to the SourceWire press release there are several reasons ATMs have become less secure. One of them is the way in which ATMs operate. ATMs hardware platforms with proprietary software and communications protocols have been migrated to commodity-embedded hardware platforms (essentially PC-based with Intel microprocessors), commodity operating systems (primarily Window and Linux), and standard IP networking. “70 per cent of current ATMs are now based on PC/Intel hardware and commodity operating systems (mostly Windows XP embedded) and this trend is expected to continue. Essentially, these new ATMs are PCs that are running PC operating systems, using the standard Internet Protocol (IP) with some additional peripherals housed in a secure vault-like box.”
No change is done if there are not advantages in the newer system. Among the advantages of the new system are: cost; performance; flexibility; standardization and enhanced functionality
And there is no coin with one side. Advantages are faded by threats the name of that is “hackers.”
2008 analysis of ATM network traffic by Network Box “found that only the PIN number was encrypted and that a large portion of the traffic travelled in plain text, leaving card numbers, card expiry dates, transaction amounts and account balances clearly readable. Therefore, a hacker needs only to access some part of the IP network between the IP-ATM and the payment processor to be privy to the aforementioned details.”ATM finds the most effective way to solve the issues is to use a multifunction device with:
Routing,
Firewall,
IDS/IPS,
VPN capabilities,
Protecting, the ATM network.
The specifics of the network are:
Separate from the rest of the bank’s network, monitor and control.
Encrypt all traffic coming out of the ATM machinesThe growth of the ATM marketAccording to SourceWire Mark Webb-Johnson, CTO of Network Box, comments: “Most people simply assume that because an ATM is invariably provided by a bank, the transactions and the data being transmitted must be secure. This assumption may have been true in the past, but today ATMs operate in a way that makes them far more susceptible to attack. “We’ve already seen in August 2003 how the Nachi (aka Welchia) Internet worm crossed over into ‘secure’ networks and infected ATMs for two financial institutions; and we’ve witnessed the SQL Slammer (aka Sapphire) worm indirectly shutdown 13,000 Bank of America ATMs. The chances are that if banks don’t use technology that can actually provide an effective level of protection – technology that is already on the market – then it is very likely that more high-profile attacks are to follow.”
 Microsoft is warning Windows Vista users that a forthcoming service pack for the operating system may stop some third-party programs working. The software giant has released a list of programs that may be broken by the SP1 update for
Microsoft is warning Windows Vista users that a forthcoming service pack for the operating system may stop some third-party programs working. The software giant has released a list of programs that may be broken by the SP1 update for The Windows Vista update will be released to the public in mid-March. Service Packs are among the biggest updates Microsoft issues for its various operating systems. The software firm said SP1 makes Vista more secure and reliable and introduces some new features.
Microsoft has also been forced to withdraw an update to
 We ask thousands of questions every day, right? Right. And these questions are more and more focused on the specific fields like arts, business, law, money, health that mostly depends on our professional education and ineterests. And I am sure everybody knows the abbreviation FAQ-Frequently Asked Questions. There are so many web sites to find the corresponding answer to the question that one can ask?! Media sources that are so much segmented offer specific users the information one seeks and that catch the audience so important in media.
We ask thousands of questions every day, right? Right. And these questions are more and more focused on the specific fields like arts, business, law, money, health that mostly depends on our professional education and ineterests. And I am sure everybody knows the abbreviation FAQ-Frequently Asked Questions. There are so many web sites to find the corresponding answer to the question that one can ask?! Media sources that are so much segmented offer specific users the information one seeks and that catch the audience so important in media.Few sites include all spheres together. Few people are able to answer each of the questions that might appear in our minds and few can say “ASK ME” leaving the space to write the question in and encourage to click “Search.” The ASK ME HELP DESK offers answers to all questions that would be provided by the experts. To receive answer to the asked question one can by free registration. It will help to:
Get free answers from experts in any of our 300+ topics.
Accept money for answers that you provide.
Communicate privately with other members (PM).
See fewer ads.
According to the ASK ME the site has 129900 members.
Ask "ASK ME" and receive answers from experts.
 Gamers will soon be able to interact with the virtual world using their thoughts and emotions alone. A neuro-headset which interprets the interaction of neurons in the brain will go on sale later this year.
Gamers will soon be able to interact with the virtual world using their thoughts and emotions alone. A neuro-headset which interprets the interaction of neurons in the brain will go on sale later this year."It picks up electrical activity from the brain and sends wireless signals to a computer. It allows the user to manipulate a game or virtual environment naturally and intuitively“ - said Tan Le, president of US/Australian firm Emotiv.
The brain is made up of about 100 billion nerve cells, or neurons, which emit an electrical impulse when interacting. The headset implements a technology known as non-invasive electroencephalography (EEG) to read the neural activity.
Ms Le said: "Emotiv is a neuro-engineering company and we've created a brain computer interface that reads electrical impulses in the brain and translates them into commands that a video game can accept and control the game dynamically."
Headsets which read neural activity are not new, but Ms Le said the Epoc was the first consumer device that can be used for gaming. "This is the first headset that doesn't require a large net of electrodes, or a technician to calibrate or operate it and does require gel on the scalp. It also doesn't cost tens of thousands of dollars. " - she said.
The use of Electroencephalography in medical practice dates back almost 100 years but it is only since the 1970s that the procedure has been used to explore brain computer interfaces.
The Epoc technology can be used to give authentic facial expressions to avatars of gamers in virtual worlds. For example, if the player smiles, winks, grimaces the headset can detect the expression and translate it to the avatar in game. It can also read emotions of players and translate those to the virtual world. "The headset could be used to improve the realism of emotional responses of AI characters in games," - said Ms Le.
"If you laughed or felt happy after killing a character in a game then your virtual buddy could admonish you for being callous," - she explained.
The $299 headset has a gyroscope to detect movement and has wireless capabilities to communicate with a USB dongle plugged into a computer. The Emotiv said the headset could detect more than 30 different expressions, emotions and actions.
They include excitement, meditation, tension and frustration; facial expressions such as smile, laugh, wink, shock (eyebrows raised), anger (eyebrows furrowed); and cognitive actions such as push, pull, lift, drop and rotate (on six different axis).
Gamers are able to move objects in the world just by thinking of the action. Emotiv is working with IBM to develop the technology for uses in "strategic enterprise business markets and virtual worlds"
Paul Ledak, vice president, IBM Digital Convergence said brain computer interfaces, like the Epoc headset were an important component of the future 3D Internet and the future of virtual communication.
- Sensors respond to the electrical impulses behind different thoughts; enabling a user's brain to influence gameplay directly;
- Conscious thoughts, facial expressions, and non-conscious emotions can all be detected;
- Gyroscope enables a cursor or camera to be controlled by head movements;
- The headset uses wi-fi to connect to a computer.
 According to the study of Brigham and Women’s Hospital the guarantee of living past 90 is abstaining from smoking, weight management, blood pressure control, regular exercise and avoiding diabetes.
According to the study of Brigham and Women’s Hospital the guarantee of living past 90 is abstaining from smoking, weight management, blood pressure control, regular exercise and avoiding diabetes.Studies of twins have found that about one-fourth of the variation in human life span can be attributed to genetics. That leaves about 75 percent that could be attributed to modifiable risk factors.
The Brigham and Women’s Hospital announces that the researchers estimate that a 70-year-old man who did not smoke and had normal blood pressure and weight, no diabetes and exercised two to four times per week had a 54 percent probability of living to age 90.
Sedentary lifestyle, 44 percent
Hypertension (high blood pressure), 36 percent
Obesity, 26 percent
Smoking, 22 percent
Three factors, such as sedentary lifestyle, obesity and diabetes, 14 percent
Five factors, 4 percent
 A controversial website that allows whistle-blowers to anonymously post government and corporate documents has been taken offline in the
A controversial website that allows whistle-blowers to anonymously post government and corporate documents has been taken offline in the However, the main site was taken offline after the court ordered that Dynadot, which controls the site's domain name, should remove all traces of wikileaks from its servers. The court also ordered that Dynadot should "prevent the domain name from resolving to the wikileaks.org website or any other website or server other than a blank park page, until further order of this Court." Other orders included that the domain name be locked "to prevent transfer of the domain name to a different domain registrar" to prevent changes being made to the site.
Wikileaks claimed that the order was "unconstitutional" and said that the site had been "forcibly censored".
The case was brought by lawyers working for the Swiss banking group Julius Baer. It concerned several documents posted on the site which allegedly reveal that the bank was involved with money laundering and tax evasion. The documents were allegedly posted by Rudolf Elmer, former vice president of the bank's
The court hearing took place last week and Dynadot blocked access from Friday evening. Wikileaks says it was not represented at the hearing because it was "given only hours notice" via e-mail. A document signed by Judge Jeffery White, who presided over the case, ordered Dynadot to follow six court orders.
As well as removing all records of the site form its servers, the hosting and domain name firm was ordered to produce "all prior or previous administrative and account records and data for the wikileaks.org domain name and account". The order also demanded that details of the site's registrant, contacts, payment records and "IP addresses and associated data used by any person...who accessed the account for the domain name" to be handed over.
Wikileaks allows users to post documents anonymously. The site was founded in 2006 by dissidents, journalists, mathematicians and technologists from the
 According to PC WORLD the spam message tricking the users interested in Hillary Clinton’s campaign speech appeared on Thursday. Doug Bowers, Symantec’s senior director of anti-abuse engineering, says that “It is the first time we have seen the spam like this targeting Hillary Clinton.”
According to PC WORLD the spam message tricking the users interested in Hillary Clinton’s campaign speech appeared on Thursday. Doug Bowers, Symantec’s senior director of anti-abuse engineering, says that “It is the first time we have seen the spam like this targeting Hillary Clinton.”The victims of the trick download a Trojan to their desktops thinking they are provided with the speech, the purpose of that is sending more and more spams.
According to Symantec the only other candidate being abused for malware purposes in this way is Ron Pau. Neither Barack Obama nor John McCain have had names exploited by Malware.
 According to Nielsen Online report for UK net ratings in 2007 BeatThatQuote.com sees Facebook off in the battle for the UK’s fastest growing website.
According to Nielsen Online report for UK net ratings in 2007 BeatThatQuote.com sees Facebook off in the battle for the UK’s fastest growing website. Four large newspaper companies are joining forces to sell advertisements on the Internet, hoping that the combined heft of their Web sites will encourage large advertisers to spend more money.
Four large newspaper companies are joining forces to sell advertisements on the Internet, hoping that the combined heft of their Web sites will encourage large advertisers to spend more money.Each of the four companies - the Tribune Company, the Gannett Company, the Hearst Corporation and The New York Times Company - is transferring a portion of its online ad space to quadrantONE, a new company that will be announced Friday.
The purpose of the joint venture, which will be based in
Some of the companies’ flagship sites, however, will not be included, because they are not considered local. These include the sites of
In total, quadrantONE will be able to reach about 50 million unique visitors a month, its executives said, citing Nielsen Online data.
The effort is at least the third in the last decade involving major newspaper companies joining forces to sell online ads. But quadrantONE comes as newspaper companies are being wooed by companies like Google, Microsoft and Yahoo, which would like to sell premium ads on the newspapers’ sites.
“We want to control our own destiny,” - said Lincoln Millstein, senior vice president for digital media at Hearst Newspapers.
Executives involved said the newspaper companies understand the local market better than Google, Yahoo and Microsoft and can best help national advertisers place their messages on local sites.
But not everyone agrees.
“I don’t think the alignment of newspaper companies will solve the issue,” - said Shar VanBoskirk, an analyst who covers online advertising at Forrester Research. “They need that alignment with a technology company that will bring them the set of skills that they need to monetize their content.”
Several of the newspapers involved in quadrantONE are part of Yahoo’s newspaper consortium, which provides advertising technologies and sales, and all of the companies are partial owners of the Newspaper National Network, a network that allows national advertisers to place ads across thousands of papers’ print editions and, more recently, Web sites. The companies were also all part of the New Century Network in the late 1990s, which failed.
Executives at the newspaper companies said quadrantONE will fare differently because it will have a central repository of advertising inventory, and thus will not have to call the newspapers individually to fill each order.
The group is inviting other newspapers to submit ad inventory, though not to join as owners.
 FileMaker that develops award-winning database software announced the availability of certification testing for the award winning FileMaker 9 product line. It gives developers opportunity gain recognition as a database industry expert. The pass of the tests also gives opportunity to use the logo on cards.
FileMaker that develops award-winning database software announced the availability of certification testing for the award winning FileMaker 9 product line. It gives developers opportunity gain recognition as a database industry expert. The pass of the tests also gives opportunity to use the logo on cards.According to FileMaker: "Databases allow you easily and quickly to share information. A simple way of sharing is to export data to PDF files or spreadsheets and then email the files to team members, business partners or friends.
Full-featured databases (such as FileMaker Pro) enable multiple people to open and use the same database at the same time. Security features allow you to limit access to information to only those who need to know."
 As FileMaker President Dominique Goupil said the FileMaker 9 has the features that are more time efficient as it needs shorter time and enable developers to add more value to their FileMaker solutions. Through FileMaker 9 the skills transfer into competitive and career advantages.
As FileMaker President Dominique Goupil said the FileMaker 9 has the features that are more time efficient as it needs shorter time and enable developers to add more value to their FileMaker solutions. Through FileMaker 9 the skills transfer into competitive and career advantages.According to the PC WORLD there are no prerequisites for the Developer Essentials for FileMaker 9 certification exam, FileMaker recommends to take FileMaker Training Series available for $129AUD. They include 12 in-depth training modules, demo files, exercises and videos. The tests are in 2 languages English and Japanese.
The official site of FileMaker comments on the use of database:
Manage your contacts and customer lists
Track projects and tasks
Create home inventory with photos
Coordinate group activities
Create quick and easy reports
Organize a charity auction
Track employee information
Print invoices, letters and mailing labels
Connect data; students and classes
Store digital assets and their descriptions
 Notorious 20th-century bank robber Willie Sutton said famously, "I rob banks because that's where the money is." It seems 21st-century criminals are following his footsteps.
Notorious 20th-century bank robber Willie Sutton said famously, "I rob banks because that's where the money is." It seems 21st-century criminals are following his footsteps.But while Sutton disguised himself as a cop, a window washer and a
One sneaky thing some malware (malicious threats) does is to modify a user's server information. For example, a user types www.bankofamerica.com into his or her browser. But instead of the computer using the service provider's server, which would take the user to the real Bank of America server, the computer uses a bogus server run by phishers and that takes the user to a fake Bank of America server. The phishers take the user's login information and empty the account. Most users, even the savvy ones, wouldn't know that their server settings have been hijacked.
Just a few years ago, computer viruses and worms seemed designed for bragging rights and a hacker's 15 minutes of fame, but the game has changed. Now, instead of creating chaos by shutting down or paralyzing computer systems, the bad guys are getting more bang for their buck by taking over systems and using them to commit crimes.
The IBM Internet security report shows that nearly 90 percent of all vulnerabilities allow this type of remote exploitation.
"The authors [of this malware] realize they are better off as parasites than they are killing their hosts," - said Chris Rouland, engineer and chief technology officer for IBM Internet security.
Rouland said that some other malicious trends include growth in Web browser exploitation, especially for Windows Internet Explorer and Mozilla Firefox. He said that although fewer vulnerabilities were disclosed publicly last year, the number of "high-severity vulnerabilities" increased by 28 percent compared with 2006.
The X-Force collected and analyzed 410,000 new malware in 2007. That's a third more than they analyzed in 2006. And wildly popular social networks like MySpace and Facebook are now prime targets for exploits.
What's an average computer user to do?
Though tech-savvy, proudly paperless home computer users may shun those so-20th-century snail mail bank statements, it might be worth it to go retro and compare your online banking information with the paper record.
Rouland says criminals in
Usually, banks give only 90 days to remediate an account problem. In the old days of worms and viruses and denial of service attacks, many of us learned, often the hard way, that computer security was often an afterthought compared to "user friendliness."
But these days, with organized criminals around the globe stealing with such great stealth, the bank with the best security might turn out to be the big business winner.
 Hey, tomorrow is Valentine’s Day!!!!!
Hey, tomorrow is Valentine’s Day!!!!! What to do?
What to say?
How to express?
While I was writing this post, different ideas came to my mind, several times I have typed and retyped the first sentence.
But later there was a sparkle, remembered my friend who pronnounced “I Love You” to her sweetheart in all languages that exist in the world. Do not you think it is just perfect?!
We have only one day before St. Valentine’s Day but for the sake of Love, those who really love can remember “I Love You ” in:
AFRIKAANS ek het jou lief / ek is lief vir jou
ALBANIAN të dua
ALSATIAN ir liàb dir Dialectal
ARABIC (North African) n'bghick Dialectal
ARABIC (Eastern) bahebbak (à un homme) / bahebbik (à une femme) Literary
ARABIC ouhibbouka (à un homme) / ouhibbouki (à une femme)
ARMENIAN yes kez siroumem
ASTURIAN quiérote
AZERI men seni sevirem
BAMBARA né bi fè
BASQUE maite zaitut
BAOULE mi klôa
BELARUSIAN Кахаю цябе (kahaju ciabie)
BENGALI aami tomakey bhalo basi
BERBER righ kem
BOBO ma kia bé nà
BOSNIAN volim te
BRETON karout a ran ac'hanout / da garout a ran / me az kar
BULGARIAN обичам те
BURMESE nga nin ko chit te
CATALAN t'estimo
CHEYENNE néméhotâtse
CHINESE wo ai ni
CORSICAN amu tè / ti tengu caru
CROAT volim te
CZECH miluji tě
DANISH jeg elsker dig
DIOULA mi fê
DUTCH ik hou van jou
ESPERANTO mi amas vin
ESTONIAN ma armastan sind
FAROESE eg elski teg
FINNISH minä rakastan sinua
FLEMISH ik hou van jou / ik heb je lief
FRENCH je t'aime
FRISIAN ik hâld fan dy
FRIULAN o ti vuei ben
GALICIAN amo-te / ámote / quero-te / quérote
GEORGIAN me shen mikvarkhar
GERMAN ich liebe Dich
GREEK s'agapo
GUARANÍ rojhayhû
GUJARATI hun tane prem karun chhun
HAITIAN CREOLE mwen renmen'w / mouin rinmin'w
HAWAIAN aloha wau ia oi
HEBREW ani ohev otakh (man to woman)ani ohevet otkha (woman to man)
HINDI main tumse pyar karta hoo
HUNGARIAN szeretlek
ICELANDIC ég elska þig
INDONESIAN saya cinta padamu / saya cinta kamu
IRISH GAELIC tá grá agam duit
ITALIAN ti amo
JAPANESE aishitemasu / aishiteru (barely used) anata ga daisuki desu ("cute")
KABYLIAN hamlagh-kem (man to woman) hamlaghk (woman to man)
KANNADA naanu ninnanna pritisutteney
KHMER bang srolaïgn ôn (man to woman) ôn srolaïgn bang (woman to man)
KINYARWANDA ndagukunda
KOREAN saranghe
KURDISH ez te hez dikim
LAO khoi hak tchao lai
LATIN te amo
LATVIAN es tevi mīlu
LEBANESE b'hibik (man to woman) b'hibak (woman to man)
LIGURIAN mi te amu
LINGALA na lingi yo
LITHUANIAN aš tave myliu
LOW SAXON ik hou van ju
LUXEMBOURGEOIS ech hun dech gäer
MACEDONIAN te sakam
MALAGASY tiako ianao / tia anao aho (stronger)
MALAY aku cinta padamu
MALAYALAM yenikku ninne estamaanu
MALTESE inhobbok
MANX ta graih aym ort
MAORI kei te aroha au i a koe
MONGOLIAN Би чамд хайртай (bi chamd khairtai)
MORÉ mam nong-a fo
NAPOLETANO t'ammo
NDEBELE niya ku tanda
NEPALI ma timilai prem garchhu
NORWEGIAN jeg elsker deg
OCCITAN t'aimi
PAPIAMENTU mi ta stima bo
PERSIAN dustat dâram (formal) / duset dâram (informal)
POLISH kocham cię
PORTUGUESE eu te amo / amo-te (informal)
PUNJABI mein tenu pyar karda han (male speaker) mein tenu pyar kardi han (female speaker)
QUECHUA de CUZCO munakuyki
RAPA NUI hanga rahi au kia koe
ROMANI kamaù tut ROMANIAN te iubesc
RUSSIAN Я тебя люблю (ia tibia lioubliou)
SAMOAN ou te alofa ia te oe SANGO mbi yé mô
SARDINIAN deo t’amo (logudorese) / deu t’amu (campidanese)
SCOTTISH GAELIC tha gaol agam ort / tha gaol agam oirbh
SERBIAN volim te
SHONA ndinokuda
SINDHI moon khay tu saan piyar aahay
SLOVAK ľúbim ťa / milujem ťa
SLOVENIAN ljubim te / rad te imam (male speaker) / rada te imam (female speaker)
SOBOTA volim te / se te volime (lit.)
SOMALI waan ku jecelahay
SONINKÉ na moula
SPANISH te amo / te quiero
SUSU ira fan ma
SWAHILI nakupenda
SWEDISH jag älskar dig
TAGALOG mahal kita
TAHITIAN ua here vau ia oe
TAJIKI jigarata bihrum duhtari hola (man to woman) tra lav dorum (woman to man)
TAMIL naan ounnai kadali-karen
TATAR min sine yaratam
TELUGU nenu ninnu premisthunnanu
TETUN hau hadomi o
THAI ผมรักคุณ (phom rak khun) - man speaking ฉันรักคุณ (chan rak khun) - woman speaking TIBETAN na kirinla gaguidou
TURKISH seni seviyorum
TURKMEN seni söýärin
UDMURT mon tone jaratiśko
UKRAINIAN Я тебе кохаю (ia tebe kohaiu)
URDU mein tumse mohabbat karta hoon (man to woman)main tumse mohabbat karti hoon (woman to man)mujhe tum se pyar heh
UZBEK seni sevaman
VENETIAN t'amo
VIETNAMESE anh yêu em (man to woman)em yêu anh (woman to man)
WALOON (orthographe à betchfessîs) dji vs voe voltî
WELSH rydw i'n dy garu di
WEST INDIAN CREOLE mwen enmen
WOLOF nob nala
YIDDISH ich hob dir lib
Though “I love you” only in Georgian is absolutely enough for me, may be in Russian, too, or French, Spanish, Italian. Well in other languages I will need this list that is provided by My Opera.
As for the business and statistics view of the Valentine’s Day, that is expected to be on the 14th of February, the National Retail Federation (NRF) reveals the results of the study and announces that the average consumer plans to spend $122.98 on Valentine's Day, up from $119.67 in 2007. Total retail spending for the Feb. 14 holiday is expected to reach $17.02 billion. Interested whether you will be given a gift day after tomorrow or not? Well, NRF says that of the 61 percent of consumers who are planning to celebrate Valentine's Day this year, nine of ten will spend the most on their significant others or spouses.
But what about other loved ones? NFR will not disappoint those loved ones too and six in ten plan to buy something for their family members, and two in ten said they would send a gift to friends.
According the NRF, this year, over 48% plan to celebrate the day by taking their significant others for a special night out, up from 45% in 2007, The same source says that nearly 48% of consumers plan to purchase candy, 36% buy flowers, and 17% - jewelry.
Of course, it is important that the recipient knows who his or her special admirer is - 57% of those surveyed plan on buying a card for their Valentine, the NRF said.
"Valentine's Day is a great time to get creative with gift options," said NRF President and CEO Tracy Mullin. "Most people agree that it's the thought that counts, but shelves will also be filled with traditional gifts for those who want to celebrate the old-fashioned way."
Study shows that men will outspend women this year, spending an average of $163.37 on gifts and cards, compared to an average of $84.72 spent by women. And I like this. ;-)
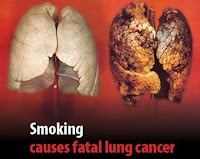 One billion people will die from tobacco-related causes by the end of the century if current consumption trends continue, according to a global report released by the World Health Organization (WHO).
One billion people will die from tobacco-related causes by the end of the century if current consumption trends continue, according to a global report released by the World Health Organization (WHO).At a press conference held in midtown
The 369-page WHO Report on the Global Tobacco Epidemic, 2008, bound like a high school yearbook and bundled with a "cigarette pack" of colored markers, called on governments to adhere to six tobacco control policies it calls MPOWER: monitor tobacco use; protect people from secondhand smoke; offer help to people who want to quit; warn about the risks of smoking; enforce bans on cigarette advertising; and raise tobacco taxes. The report also breaks down tobacco consumption and prevention efforts country by country. To date, it is the most comprehensive study of its kind at a global level, said
The collected data should equip countries around the world to begin implementing anti-tobacco policies, Chan says, including smoking bans, aggressive anti-tobacco campaigns and massive tobacco tax hikes. According to the report, nearly two thirds of the world's smokers live in 10 countries - China, India, Japan, Indonesia, Bangladesh, the U.S., Brazil, Germany, Russia, and Turkey.
According to the study, the most effective tactic globally has been simply to raise prices. Lower income people smoke significantly more than the wealthy, and spend a much higher proportion of their income on tobacco - 20% of the most impoverished households in
Another vulnerable group: women. Though women still smoke at just one quarter the rate of men, tobacco advertisers are increasingly targeting this largely untapped market. Among adolescents in European Union member nations, girls may now be even more likely to smoke than boys. Globally, Chan said, "the rise of tobacco use among girls and young women is among the most ominous trends."
As with virtually all public-health problems, a major hurdle to reducing smoking, the study said, is lack of public education. People are not fully aware of the hazards of smoking, and it's a weakness that the tobacco industry is quick to exploit, Bettcher said.
Asked whether he would back a federal ban on smoking in the workplace or public spaces, Bloomberg said he would, but added, "I don't think the federal government should prohibit the manufacture or sale of cigarettes," but that combatting tobacco should mean diminishing the demand.
Once a smoker himself, Bloomberg said he was able to quit only when he truly understood the consequences. "As I became more mature and started thinking, 'Do I want to live or not?' it was an easy decision." For those who want to smoke, however, he feels it should be their right, so long as they aren't harming others. "I happen to agree with those who think you have a right to kill yourself," he said.
 1,300 students from Dallas Baptist University are going to commit 28 minutes audio support to listen to the bible in 40 days at a chapel service. The campaign that is called You’ve Got The Time DBU, is using Audio New Testaments from Faith Comes By Hearing, the world's leading Audio Bible ministry.
1,300 students from Dallas Baptist University are going to commit 28 minutes audio support to listen to the bible in 40 days at a chapel service. The campaign that is called You’ve Got The Time DBU, is using Audio New Testaments from Faith Comes By Hearing, the world's leading Audio Bible ministry.According to Dr. Bob Garrett, a DBU graduate program director and You've Got The Time DBU organizer, every attendee of the chapel service received a free New Testament on MP3 disc. He said the chapel students will listen from Matthew 1 to Revelations 22 starting now and going until Easter-announces PRWEB.
"We want to help young people draw closer to God by hearing His Word," Garrett said. "We also want them to help others get closer by sharing His Word. The Bible is not just for us, it's for the nations, and we want the students to have an international agenda," he said.
According to the PRWEB Jerry Jackson, Faith Comes By Hearing Founder and President, said he is also praying that "God's Word will help grow the faith of not only the students but also the whole college community."
"I am very excited about this historic university teaming up with Faith Comes By Hearing to promote God's Word in audio and influence the next generation of Christian leaders," said Jackson.










